Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
The most fundamental and direct security defense portal.
The Domain Name System (DNS) is an essential service in an enterprise-level organization and is often overlooked by management. iSafer’s exclusive design able to ensures the system operation and security of DNS service by supporting multiple and flexible query limit control policy.
The threshold control offers the ability to limit by query name or source; once query numbers exceed the threshold given, iSafer will force drop additional matching queries. In most circumstances, the threshold control would be sufficient to mitigate most targeted application DDoS attacks from inside endpoint, rather than an expensive DDoS inspection gateway at WAN point, at makes even fast and effective of protection.


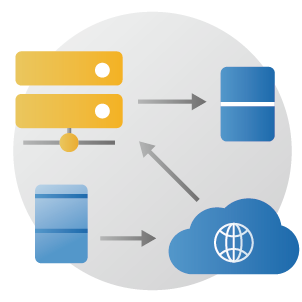
In the cloud service environment, the originally designed failover mechanism will bring huge delays when reaching the service host, such as telemedicine, crewless construction, or electromechanical operations, etc., may be affected by 5G network transmission.
iSafer supports failover with load balance and health monitoring, organization can now monitor backend DNS service using actual queries on certain resource records. If any backend DNS service has been markdown by the health monitor, service will auto shift to one marked as alive. Furthermore, iSafer able to distribute queries follow load balance policy to service servers in order to shorter the response time, resulting in customer experiences and service uninterrupted.
OS vendors have recently added support to the DoH protocol. However, to adding a new protocol means going through a complex and cumbersome update process; the chaotic experience of juggling the coexistence of IPv6 and IPv4 is enough to make the most experienced of IT admins shudder.
Offering a DNS reverse proxy feature module that supports advanced security standards such as DoH, DoT, and DNSCrypt, URMAZI’s iSafer is well-equipped to perform conversion and communication between existing and new protocols. It assists administrators in achieving a higher level of security without undertaking the complex procedures or the risks of rebuilding or updating the current Domain Name Systems.

The original DNS framework had no security: basically, anyone could query anything. IT Admins also had to frequently modify and restore DNS configuration files just to perform any type of service maintenance, testing, troubleshooting, or any other temporary tasks. This frequent overwriting of configuration files often resulted in plenty of unnecessary manual work and increased errors.
iSafer resolves these issues by implementing an Access Control List (ACL), this can grant or deny access. However, it also offers a multitude of advanced controls.
ACL can significantly enhance the security and flexibility of an enterprise’s DNS service.
SafeSearch is a safety feature found in popular search engines, such as Google, Bing, and Youtube. If enabled, the search engine pre-filters search and web results to block explicit content like violence, pornography, etc.
However, enabling SafeSearch requires users to manually toggle the setting for each search engine. Search engines may also refer to SafeSearch under different names, requiring users to navigate a hierarchy of configuration options to find it.
iSafer’s SafeSearch feature simplifies the process of enabling SafeSearch for all supported search engines, requiring admins to activate just a single rule. This eliminates the need to toggle individual settings for each browser, making it easier to implement a unified security regulation that protects your young ones from inappropriate content.




Threat intelligence is one of the best ways for organizations to filter harmful sources, ensuring they stay well-informed and prepared to face unknown malicious attacks without fear. As hacker groups have transformed ransomware-as-a-service (RaaS) into a business model and established their own ecosystem, the scope of malicious partnerships and infected targets has rapidly expanded. Therefore, threat intelligence must come from diverse geographical and industrial sources to effectively defend against various hidden threats.
iSafer offers users a personalized threat intelligence subscription service, utilizing deep learning and artificial intelligence technologies to collect and analyze the latest global domain threat intelligence. It automatically categorizes the data into 58 different types, enabling IT administrators to accurately monitor organizational network activities and adjust more suitable security policies. This way, the service can effectively protect against malicious sources like botnet, scams, phishing, and ransomware.
The threat intelligence subscription service provides organizations with 24/7 uninterrupted content updates, ensuring users have access to the latest global defense capabilities in real-time.
DNS Sinkhole is a technique used to redirect traffic from malicious websites or domains to a non-existent IP address, effectively blocking access to these sites. This technique helps to prevent malware, viruses, and other cyber threats from infiltrating your network.
iSafer DNS Sinkhole helps to block malicious traffic from reaching your network by redirecting it to a non-existent IP address. By preventing access to malicious domains, it effectively blocks threats such as malware, viruses, and other cyber attacks from infiltrating your network.
Besides preventing malicious access, Sinkhole can be used to identify compromised hosts by analyzing the sinkhole logs and identifying hosts that are trying to connect to known malicious domains. For example, if the logs show that one particular machine is continuously attempting to connect to a C2 server, but the request is being redirected because of the sinkhole, then there is a good chance that this particular machine is infected with a bot.


Many malicious attacks, including DDoS, involve persistent querying of specific DNS record types, names, server versions, or special characters before launching an attack. The goal is to assess the target’s DNS security defenses and vulnerabilities, acting opportunistically.
iSafer’s “Dynamic Block” is an advanced real-time defense mechanism. The system assesses the behavior of all query sources, making determinations and automatically blocking high-risk threat connections at a per-second rate. This proactive and automated protection enables organizations to preemptively guard against potential large-scale attack opportunities.

